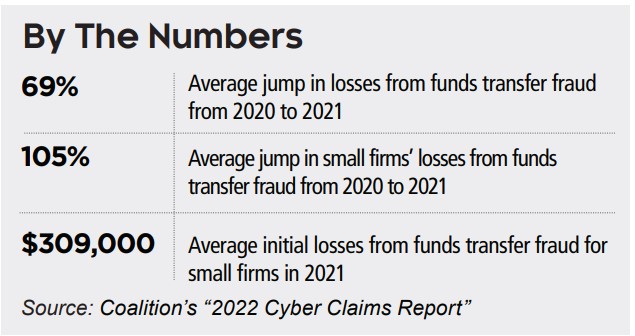
WHILE RANSOMWARE is making the headlines as the major cyber threat, small and mid-sized businesses are increasingly being targeted by lower fraud that dupes them into wiring criminals funds, according to a new report.
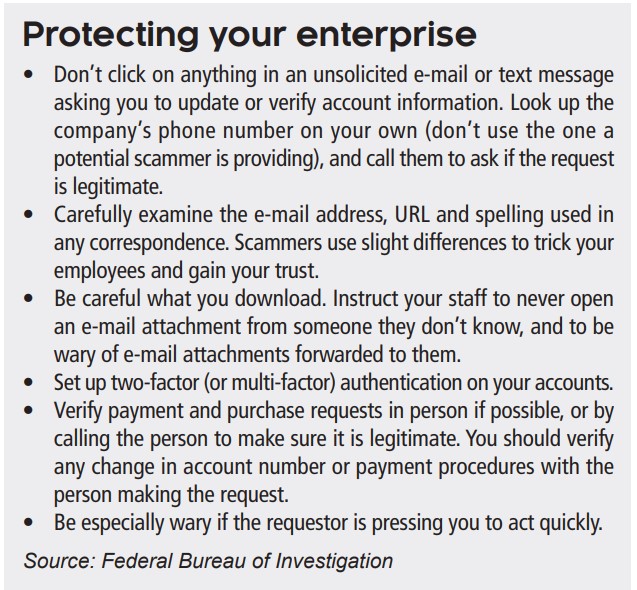
These funds transfer fraud crimes involve hackers gaining access to a firm’s mailbox and extracting payments that go into their accounts. Companies should have in place proper systems safeguards to combat these attacks, and that includes regularly training staff on how to identify these attempts to steal funds.
How it works
Criminals will often try to penetrate your servers by sending “spearphishing” e-mails. These messages look like they’re from a trusted sender to trick victims into revealing confidential information. They may also send malicious e-mails in the hope that an employee clicks on a bogus link. The link then releases malicious software that infi ltrates company networks and gains
access to legitimate e-mail threads about billing and invoices.
Once the criminals have access to your business mailbox, they can manipulate your contacts and modify payment instructions. They may also use their access to your systems to send e-mails that appear to come from a known source making a legitimate request.
Insurance options
The best option for coverage is a commercial crime insurance policy. Most of these policies cover acts like:
• Employee dishonesty
• Computer and funds transfer fraud
• Forgery or alteration
• Money and securities theft
• Theft of client’s property.
Some policies may exclude funds transfer fraud, or they may have lower sublimits for such acts. In such cases you may need to get a policy extension to cover the risk. There is also cyber liability insurance, which covers direct losses resulting from cyber crime. But these policies will often exclude coverage for social engineering attacks, which are the kinds that the criminals behind funds transfer fraud use. You may be able to purchase a rider to your cyber liability policy that would cover these crimes.